Opalsec :verified: · @Opalsec
175 followers · 85 posts · Server infosec.exchangeHappy Monday folks, I hope you had a restful weekend and managed to take a breather from all things cyber! Time to get back into it though, so let me give you hand - catch up on the week’s infosec news with the latest issue of our newsletter:
https://opalsec.substack.com/p/soc-goulash-weekend-wrap-up-09e?sd=pf
#Emotet are back and are using…OneNote lures? ISO disk images? Malvertising? Nah – they’re sticking with tier tried and true TTPs – their Red Dawn maldoc template from last year; macro-enabled documents as lures, and null-byte padding to evade automated scanners.
We’ve highlighted a report on the Xenomorph #Android Banking Trojan, which added support for targeting accounts of over 400 banks; automated bypassing of MFA-protected app logins, and a Session Token stealer module. With capabilities like these becoming the norm, is it time to take a closer look at the threat Mobile Malware could pose to enterprise networks?
North Korean hackers have demonstrated yet again that they’re tracking and integrating the latest techniques, and investing in malware development. A recent campaign saw eight new pieces of malware distributed throughout the kill chain, leveraging #Microsoft #InTune to deliver payloads and an in-memory dropper to abuse the #BYOVD technique and evade EDR solutions.
A joint investigation by #Mandiant and #SonicWall has unearthed a two-year campaign by Chinese actors, enabled through exploitation of unpatched SMA100 appliances and delivery of tailored payloads. A critical vulnerability reported by #Fortinet this week helps reinforce the point that perimeter devices need to be patched with urgency, as it’s a well-documented target for Chinese-affiliated actors.
#HiatusRAT is a novel malware targeting #DrayTek routers, sniffing network traffic and proxying C2 traffic to forward-deployed implants. TTPs employed in recent #BatLoader and #Qakbot campaigns are also worth taking note of, as is #GoBruteforcer, a new malware family targeting specific web server applications to brute force logins and deploy an IRC bot for C2.
Those in Vulnerability Management should take particular note of the #Veeam vulnerability, which appears trivial to exploit and actually delivers plaintext credentials to the attacker. CISA have also taken note of nearly 40k exploit attempts of a 2 year old code-exec-as-root vulnerability in the #VMWare Cloud Foundation product in the last two months, so make sure you’re patched against it.
#Redteam members have some excellent reading to look forward to, looking at HTTP request smuggling to harvest AD credentials and persisting with a MitM Exchange server, as well as a detailed post that examines #CobaltStrike’s reflective loading capability;
The #blueteam has some great tradecraft tips from @inversecos on #Azure DFIR, as well as tools to help scan websites for malicious objects, and to combat the new #Stealc #infostealer and well-established Raccoon Stealer.
Catch all this and much more in this week's newsletter:
https://opalsec.substack.com/p/soc-goulash-weekend-wrap-up-09e?sd=pf
#infosec #cyber #news #cybernews #infosec #infosecnews #informationsecurity #cybersecurity #newsletter #hacking #security #technology #hacker #vulnerability #vulnerabilities #malware #ransomware #dfir #soc #threatintel #threatintelligence #DarkWeb #mdm #dprk #FortiOS #FortiProxy
#emotet #android #microsoft #intune #byovd #mandiant #sonicwall #fortinet #hiatusrat #draytek #batloader #qakbot #gobruteforcer #veeam #vmware #redteam #cobaltstrike #blueteam #azure #stealc #infostealer #infosec #cyber #news #cybernews #infosecnews #informationsecurity #cybersecurity #newsletter #hacking #security #technology #hacker #vulnerability #vulnerabilities #malware #ransomware #dfir #soc #threatintel #threatintelligence #darkweb #mdm #dprk #fortios #FortiProxy
𝚃𝚎𝚌𝚑 𝚊𝚗𝚍 𝙲𝚘𝚏𝚏𝚎𝚎 ☕ · @techandcoffee
761 followers · 2774 posts · Server techhub.socialThreat actors are using advanced malware to backdoor business-grade routers
Hiatus hacking campaign has infected roughly 100 Draytek routers. /sp/
#Backdoor #Blacklotus #Cybercrime
#Cybersecurity #Datasecurity
#Draytek #Ethicalhacker #Exploit
#Hack #Hacked #Hacker #Hackernews
#Hackers #Hacking #IMAP
#Informationsecurity #Infosec
#Infosec #Malware #Pop #Routers
#SMTP
#backdoor #blacklotus #cybercrime #cybersecurity #datasecurity #draytek #ethicalhacker #exploit #Hack #Hacked #hacker #hackernews #hackers #hacking #imap #informationsecurity #infosec #malware #pop #routers #smtp
tkteo · @tkteo
39 followers · 1196 posts · Server infosec.exchangeto quote @ctin , "The packet capture ability of this RAT should be wake-up call for anyone sending unencrypted email."
Besides passively capturing IMAP, SMTP, and POP email, the malware also backdoors routers with a remote access Trojan that allows the attackers to download files and run commands of their choice. The backdoor also enables attackers to funnel data from other servers through the router, turning the device into a covert proxy for concealing the true origin of malicious activity.
“This type of agent demonstrates that anyone with a router who uses the Internet can potentially be a target—and they can be used as proxy for another campaign—even if the entity that owns the router does not view themselves as an intelligence target,” researchers from security firm Lumen’s Black Lotus Labs wrote. “We suspect that threat actors are going to continue to utilize multiple compromised assets in conjunction with one another to avoid detection.”
The researchers said the campaign, dubbed Hiatus, has been operating since at least last July. So far, it has primarily hit end-of-life DrayTek Vigor models 2960 and 3900 running an i386 architecture. These high-bandwidth routers support virtual private network connections for hundreds of remote workers. To date, roughly 100 routers have been infected, which is about 2 percent of the DrayTek 2960 and 3900 routers exposed to the Internet. The researchers suspect the unknown threat actor behind Hiatus is deliberately keeping its footprint small to maintain the stealth of the operation. #malware #data #security #network #email #intelligence #cybersecurity #emailsecurity #datasecurity #infosec #informationsecurity #router #routers #draytek #smtp #imap #pop3
#malware #data #security #network #email #intelligence #cybersecurity #emailsecurity #datasecurity #infosec #informationsecurity #router #routers #draytek #smtp #imap #pop3
Richard Bairwell (main) · @rbairwell
520 followers · 1491 posts · Server mastodon.org.ukDoes any one know of a customer data leakage from #Draytek?
Just had (12hrs ago) a spam email sent to an email address unique to them.
( @haveibeenpwned / @troyhunt )
Chris Glaister 🇮🇲 · @glaist
132 followers · 444 posts · Server mstdn.im@bot_mr Largely the problem is mitigated if your router does not have "management over Internet" enabled, but still, keep your devices patched, folks. #draytek #isleofman
Tristan :bisexual_flag: · @TristanBinox
73 followers · 245 posts · Server meow.socialReally happy with the way I have things setup on my home network now. Got #piHole and #dnscrypt-proxy on an inexpensive eBay mini PC (Pis are unobtainium) on name and DHCP duty. #Unraid is handling storage, streaming (Plex) and all my strictly-legal media needs. #Ubiquiti APs are a huge upgrade over the ISP supplied junk as is a #Draytek router. I think the addition of a little more structured cabling in the house and a decent #pfSense router/firewall will finish the picture.
#pfsense #draytek #ubiquiti #unraid #dnscrypt #pihole
(RTP):tor:Privacy & Tech Tips · @RTP
2616 followers · 3880 posts · Server fosstodon.orgAlso This Week:
29 Models Of Draytek Routers Vulnerability Can Allow Full Remote Compromise
#routers #hardware #exploit #Draytek #vulnerability #News
https://thehackernews.com/2022/08/critical-rce-bug-could-let-hackers.html
#routers #hardware #exploit #draytek #vulnerability #news
ITSEC News · @itsecbot
687 followers · 32461 posts · Server schleuss.onlineInside the Hoaxcalls Botnet: Both Success and Failure - The DDoS group sets itself apart by using exploits -- but it doesn't always pan out. more: https://threatpost.com/inside-hoaxcalls-botnet-success-failure/156107/ #symantecwebgateway #abandonedexploits #vulnerabilities #malwareanalysis #websecurity #grandstream #hoaxcalls #exploits #failures #takedown #malware #draytek #radware #botnet #zyxel #ddos #iot
#iot #ddos #Zyxel #botnet #radware #draytek #malware #takedown #failures #exploits #hoaxcalls #grandstream #websecurity #malwareanalysis #vulnerabilities #abandonedexploits #symantecwebgateway
DirtyTech · @dirtytech
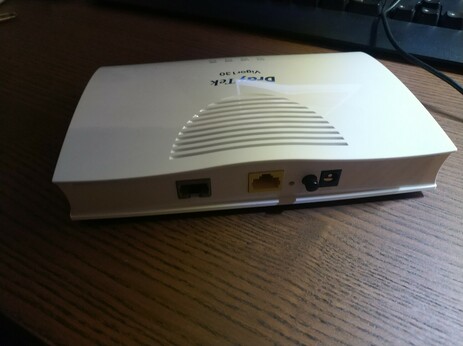
7 followers · 33 posts · Server social.tchncs.deEy #DrayTek was habt Ihr euch dabei gedacht als Ihr den Vigor 130 gebaut habt?
"Komm, lass uns den größer machen, sonst übersieht man den doch."
- "Ja, und auf keinen Fall stapelbar oder eckig, der könnte ja sonst mit irgendwas unwichtigem verwechselt werden!"
"Genau, Hardware die nicht wie ein UFO aussieht funktioniert bloß zu Hälfte, weiß mal wieder keiner..."